500.000 WooCommerce-Websites wurden gehackt
Kritischer Authentifizierungs-Bypass im WooCommerce-Payments-Plugin

Neue Sicherheitslücke in WooCommerce Payment Plugin entdeckt
Exploit auf YouTube ansehen: RASP protects website from authentication bypass
CVE Details: No CVE has yet been issued (March 28, 2023)
WooCommerce-Erklärung: developer.woocommerce.com critical vulnerability
Eine neu entdeckte Sicherheitslücke in der WooCommerce Payment Plugin has been found, which affects versions 4.8.0 bis 5.6.1. Die Sicherheitslücke hat einen CVSS-Wert von 9.8, die es als dringend kritisch einstufen. Die Ausnutzung der Schwachstelle führt zu einer vollständigen Kompromittierung des Systems, wobei Angreifer die vollständige Kontrolle über die betroffene Website erlangen..
The vulnerability exists in the “determine_current_user_for_platform_checkout” function, which uses the Wordpress "determine_current_user" filter and takes untrusted user input directly as the user id of the current user, bypassing all authentication requirements. Diese Sicherheitslücke kann genutzt werden, um sich als ein beliebiger Benutzer mit vollen Rechten auf der Website auszugeben..
Der beteiligte Sicherheitsforscher Michael Mazzolini in the HackerOne bug bounty program reported the vulnerability directly to the woocommerce team. They have decided to not issue a CVE until April 6, 2023 to allow users time to update their vulnerable software. BitFire has decided to not release the specific details on how to exploit the vulnerability while users are still updating their websites.
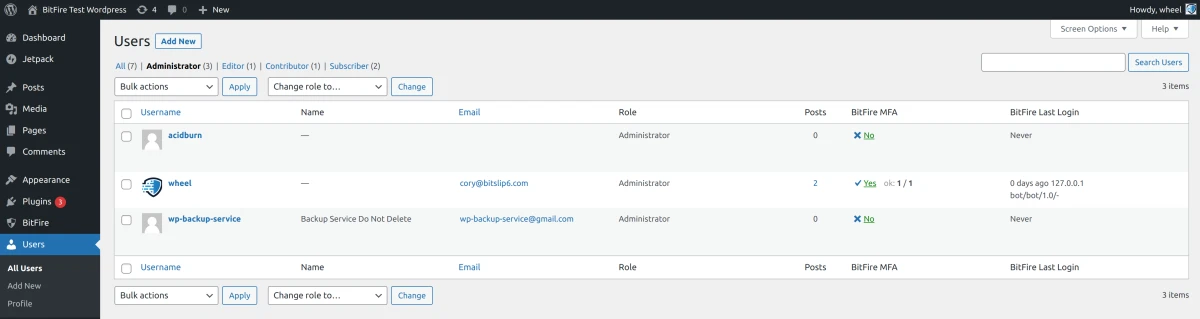
Diese Schwachstelle ist jedoch leicht auszunutzen und zu finden, und wird derzeit im Internet ausgenutzt. BitFire has seen a recent upswing in Authentication Bypass RASP firewall denies linked to this attack. Es scheint, dass mehrere Bot-Netze derzeit WooCommerce-Websites mit Exploit-Code anvisieren, um Backdoor-Konten zu erstellen. Site administrators running the WooCommerce Payment Plugin are advised to review all current user accounts on their system, change passwords, and run a complete malware scan on their website.
Benutzerkonten überprüfen
Beobachtete Angriffe versuchen, Backdoor-Administratorkonten auf anfälligen Websites zu erstellen. Administrators are urged to review all current administrator accounts on their websites. If any unknown accounts are found run a comprehensive full malware cleanup procedure.
HTTP-Zugriffsprotokolle überprüfen
We have collected some sample exploitation attempts and administrators can review logs to check for compromise attempts. Sites running the vulnerable plugin can review their HTTP access logs and look for lines similar to the following:
108.171.120.25 - - [26/Mar/2023:18:33:09 -0600] "POST /?rest_route=/wp/v2/users HTTP/1.1" 200 2283 "-" "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:111.0) Gecko/20100101 Firefox/111.0"
Beachten Sie den Antwortcode 200 und die Antwortgröße von 2200 Byte. Successful exploitation will have a similar response size in the logs. Failed exploitation due to blocking from a RASP firewall will result in a 403 resposne code indicating the attack was stopped.
Führen Sie einen vollständigen Malware-Scan durch
Nachdem Sie Ihre Website auf nicht autorisierte Administratorkonten überprüft haben, ist es wichtig, dass Sie Ihre Website auf mögliche hochgeladene Malware überprüfen.
Use a complete malware scanner like the one included with the BitFire security plugin or another high quality malware scanner like MalCure
Der Selbstschutz von Laufzeitanwendungen kann die Umgehung der Authentifizierung verhindern
Es ist wichtig zu wissen, dass herkömmliche Web Application Firewall (WAF)-Lösungen nicht in der Lage sind, diese Art von Angriffen zu blockieren. Nur eine Runtime Application Self-Protection Firewall (RASP) wie BitFire ist in der Lage, Angriffe zur Umgehung der Authentifizierung zu stoppen..
BitFire RASP prevents this attack out-of-the-box by monitoring the WordPress authentication path and requiring at least one valid authentication method has passed to allow the request. We created this You-Tube video to show exactly how this vulneraiblity is exploited and how a RASP can prevent this type of attack. RASP schützt Website vor gefährdeten Websites vor Exploits
the newly discovered security vulnerability in the WooCommerce Payment Plugin requires urgent attention from site administrators who are using this plugin. By following the recommended precautions, administrators can help to mitigate the risk of their website being compromised by attackers. Additionally, using a RASP solution like BitFire can help to provide an extra layer of protection against authentication bypass attacks.