Complete guide to scanning, understanding results, and cleaning up malware
BitFire's malware scanner protects your WordPress site by checking every file against a database of over 10,000,000 known WordPress core, plugin, and theme files. Any file that has been modified or doesn't belong is flagged for your review. Suspicious files are then evaluated using advanced machine learning to determine whether they are actual malware or harmless code.
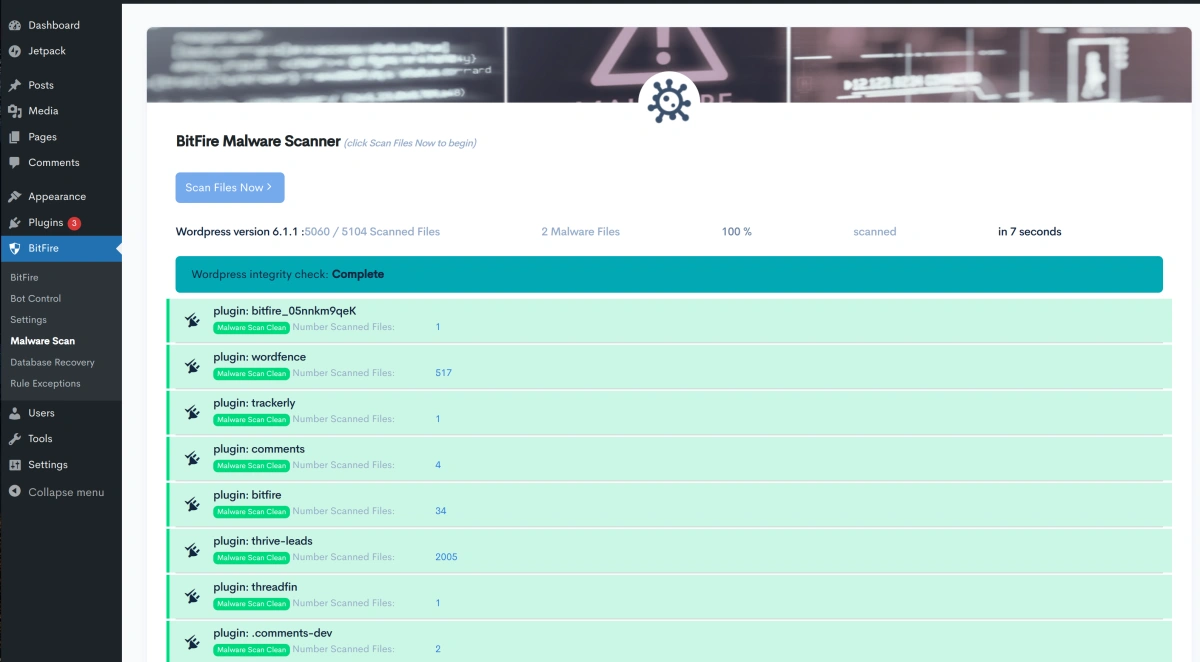
A typical WordPress site with around 10,000 files completes a scan in about 60 seconds. Subsequent scans are even faster.
If you leave the page and come back later, your previous scan results are loaded automatically — no need to rescan.
The scan runs in three steps:
Every PHP and JavaScript file on your site is fingerprinted and compared against BitFire's database of official files from WordPress.org — including core, plugins, and themes. Files that match are marked Clean and require no action.
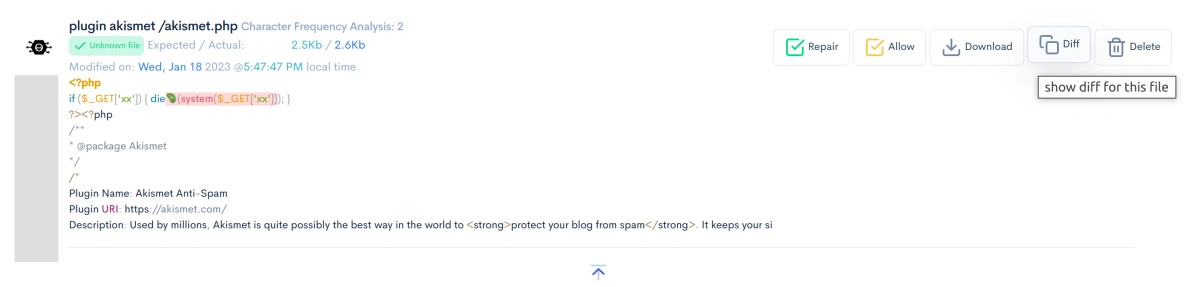
Files that exist in the official WordPress repository but have been changed are compared to the original version so you can see exactly what was modified. Files that don't exist in any repository are treated as entirely unknown.
The remaining files are evaluated using several detection signals:
| What We Check | What It Means |
|---|---|
| Character Frequency | Malware often has an unusual distribution of characters due to obfuscation |
| Unknown Variables | A high percentage of random or unreadable variable names is a red flag |
| Max Line Length | Malware tends to pack code onto extremely long lines (2,000+ characters) |
| File Size | Unusually large files (over 1 MB) may contain hidden payloads |
| Last Modified Date | A file modified at an unusual time compared to other files in the same folder |
| File Contents | Whether the file's content matches any known legitimate file |
These signals are combined into a risk score that determines each file's classification.
After a scan, a summary bar at the top shows how many files fall into each category. Files are sorted with the most dangerous first.
These files are very likely malware. They contain dangerous code such as commands that can execute programs on your server
(system(), shell_exec()), have heavily obfuscated code, or score very high across multiple detection signals.
What to do: Delete the file, or click Repair if it's a modified version of an official WordPress file.
These files have characteristics that need a closer look, but aren't as clearly dangerous as Critical files. This includes files with unusual variable names,
encoding functions like base64_decode, or suspicious JavaScript patterns.
What to do: Use AI analysis to get a second opinion before taking action.
These files are most likely safe. This category includes files whose content matches a known plugin or theme (just in an unexpected location), files with minor modifications from the official version, and files with low overall suspicion scores.
What to do: You can safely Allow these in most cases. Review the details if you want to be sure.
BitFire couldn't reach its hash server to verify these files. This usually means a temporary network issue.
What to do: Run the scan again once your server's internet connection is restored.
Each flagged file gives you several options. Click Details on any file to see the full set of actions.
Available when the file is a known WordPress core, plugin, or theme file. This downloads the original clean version from WordPress.org and replaces the modified copy on your server. This is the safest option for any file that has been tampered with.
Removes the file from your site. Use this for files that are confirmed malware and are not part of any known plugin or theme.
Don't worry — deleted files aren't gone forever. BitFire automatically quarantines files before removing them (see Restoring Quarantined Files below).
Marks the file as safe in its current state. It will be skipped in future scans. Use this when you're confident a flagged file is legitimate — for example, a custom plugin that uses unusual coding patterns.
Shows a side-by-side comparison between the official version of a file and the version on your server. Changes are highlighted, and lines that look potentially malicious are marked with a 🦠 icon. This is the best way to understand exactly what was changed.
Saves a copy of the flagged file to your computer for offline review or to share with a developer.
If you're not sure whether a flagged file is real malware or a false alarm, let BitFire's AI analyze it. The AI is trained to understand PHP and JavaScript code and can tell you whether a file is genuinely dangerous or just looks unusual.
For each analyzed file, the AI provides:
Files the AI marks as Safe with 80% or higher confidence are automatically allowed.
| Free | Pro | |
|---|---|---|
| Files per scan | Up to 10 | Up to 500 |
| Speed | Batch processing (results in 0–2 hours) | Real-time (results in seconds) |
| AI models | Smaller models | Larger, more accurate models |
Upgrade to Pro for real-time AI analysis with the most accurate models.
When you delete a file through BitFire, it isn't permanently destroyed. BitFire moves it to a quarantine folder first, so you can restore it if needed.
Quarantined files are stored at:
wp-content/uploads/bitfire_XXXXXXXXX/quarantine/
(where XXXXXXXXX is a random string unique to your installation)
Inside that folder, each quarantined file is saved with its original name plus a random extension, like:
original-file.php.a7b3fTo restore a quarantined file, use your hosting file manager or FTP client to copy it back to its original location and remove the extra extension.
If you'd like to review files manually using the Diff view, here's what to look for:
$x4a2f, $_0xabc)base64_decode, str_rot13, eval)system, exec, shell_exec)$user_email, get_post_title)Here are the most common reasons BitFire flags a file:
| What Was Found | What It Means |
|---|---|
| Dangerous function call | The file calls functions like eval(), system(), or exec() that can run arbitrary code on your server |
| Variable names look like malware | A high percentage of the variable names appear random or machine-generated |
| Modified file | A known WordPress file has been altered from its official version |
| Unknown file | A file that doesn't belong to any known WordPress core, plugin, or theme |
| Suspicious JavaScript | JavaScript code using obfuscation or packing techniques commonly seen in malware |
| fromCharCode flood | JavaScript hiding its real content by encoding it as numbers |
| Sensitive file exposed | Files like .env, private keys, or credentials that should not be accessible on your web server |
If you have WP-CLI access to your server, you can run scans from the command line:
wp bitfire malwareYou can also choose an output format:
wp bitfire malware --format=table # Human-readable table (default)
wp bitfire malware --format=json # JSON output for scripts
wp bitfire malware --format=csv # CSV for spreadsheetsThis is useful for automated monitoring, scheduled server maintenance, or if you prefer working from the terminal.
Cleaning up malware is only half the battle. Here's how to keep your site safe going forward:
About 60 seconds for a typical WordPress site with ~10,000 files. Subsequent scans may be faster.
Click Allow to mark it as safe. It won't be flagged again. BitFire's false-positive rate is approximately 1 in 2,500 files, so it's normal to see a few harmless files flagged on a typical site.
Files that couldn't be verified are marked UNVERIFIED (gray). Just run the scan again when connectivity is restored.
Generally, no. Low Risk files are most likely legitimate parts of your plugins or themes. Use AI analysis to confirm before taking action.
Free gives you batch analysis of up to 10 files with results in 0–2 hours. Pro gives you real-time analysis of up to 500 files with results in seconds, using larger and more accurate AI models.
Yes. Deleted files are quarantined, not permanently removed. See Restoring Quarantined Files for how to recover them.
Yes. If you have WP-CLI installed, run wp bitfire malware to scan from the terminal.
Use --format=table, --format=json, or --format=csv for different output formats.