BitFire Core Settings
version 4.1.10+
BitFire Ultimate WordPress Security Guide
BitFire Core Settings
The BitFire settings page allows you to enable and disable each security option provided by BitFire. BitFire FREE includes the most comprehensive Bot-Blocking features for WordPress available anywhere.
Bot Blocking is critical to your website security posture. This free tool instantly stops brute force attacks, credential stuffing attacks, SPAM, wpscan, nmap, nicko, nessus, python exploit scripts and any other hacking tool targeting your website.
TL;DR: Enable all marked options and put an end to web attacks!
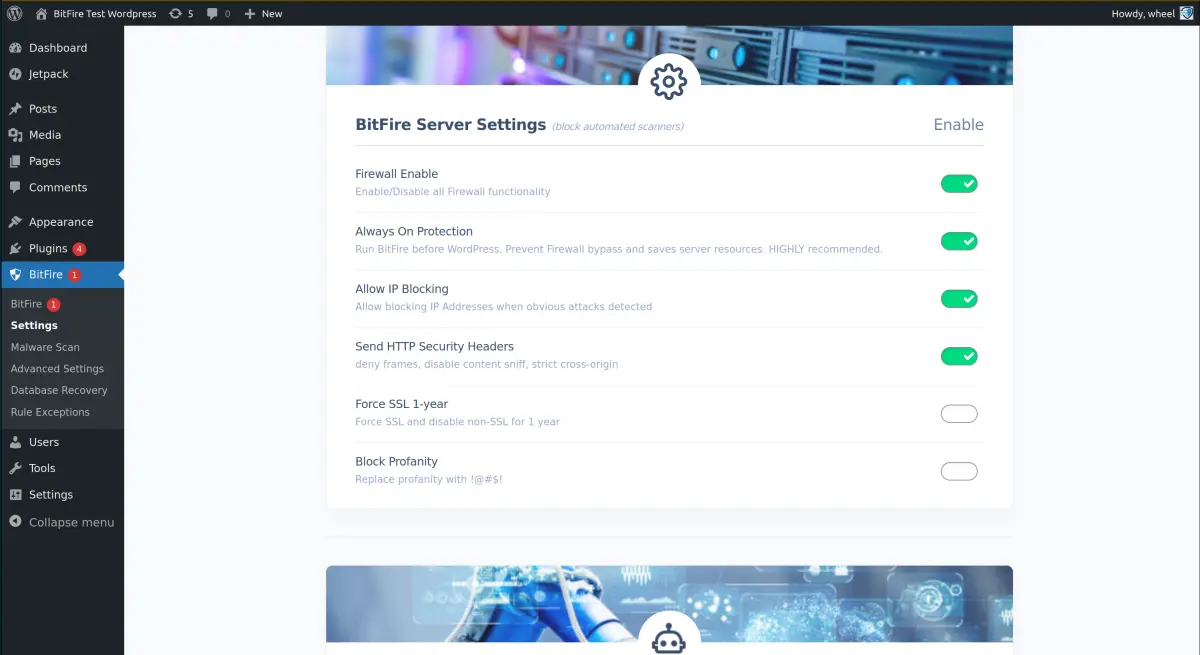
BitFire Server Settings
- "BitFire Enable": Disabling this switch will turn off all Firewall, bot-blocking, logging, header, and RASP features. This is equivalent to disabling / uninstalling the WordPress plugin without disabling it.
- "Always On Protection": Add BitFire to you user.ini auto_prepend startup. This is equivalent to WordFence "Optimize Mode". It can provide additional protection for your website. There is slight risk on some hosting providers do not support this feature well. Please ensure correct firewall functioning before enabling this feature. (5 min update time for PHP to see this change enabled or disabled)
- "Log Everything": BitFire includes a binary access log capable of logging all HTTP requests to your server. By default it will log all browser checks and blocks. Enabling this feature will tell BitFire to log ALL requests, including allowed requests. The FREE binary log size is 512 events. PRO log size is 32,000
- "Disable XMLRPC": Disabling XML RPC can increase the security of your website if you do not use it. Notable examples include JetPack integration, and the official WordPress mobile app. Notable security risks include automated login attacks. (NOTE, this are blocked with correct configuration of Bot Blocking)
BitFire Security Headers
Contrary to what many WordPress security plugins tell you. There is no XSS protection with HTTP headers . Content Security polices however provide excellent protection from XSS, redirect attacks and many other browser attacks. It can be frustrating to configure for many sites, our PRO auto-configure option is recommended for difficult WordPress configurations.
- "Send HTTP Security Headers": Send the core HTTP security headers. These options instruct the web browser how to handle data in a more secure way. And are compatible with 99% of websites.
- "Require SSL": Send and HSTS header instructing browsers to never connect to your site without using SSL. This feature is recommended for most sites, however if your SSL certificate expires, your website will not be accessible in any way until the certificate is updated.
- "Send Content Security Policy": Send a global content-security policy to web browsers not accessing your front end web content. This requires adding every domain that your sites loads resources from to the included text area. After enabling this option load your site, find what breaks and add those domains to the editable list. If possible, remove any 'unsafe-inline' resources.
- "Send Permission Policy": The permission policy controls which APIs are available on your website. This can be used to restrict access to the browser camera, microphone, geo location services, etc. Restricting this access will prevent any possibly malicious JavaScript from accessing those client mobile resources. The default option disables most additional features.
- "Deny Cross Origin Resource Sharing": This option controls how your web site will handle external web sites making dynamic requests to this site. Enabling this feature explicitly denies these potentially dangerous client side requests. Compatible with >99% of sites.
BitFire Bot Blocking
Bot Blocking is the most important feature to configure correctly for your website. Correctly identifying real browsers from fake ones and good bots from bad bots, will make it impossible to execute brute force attacks, credential stuffing, vulnerability scanning and even prevent exploits from ever connecting to WordPress. It works in 2 steps: identify browser or bot, then block what's not.
Step 1, identify browsers. BitFire has identification information for over 100 different browsers and can instantly fingerprint >95% of brewers with a single request. It's important to understand that every spam, hacking or exploit tool that uses the latest Chrome User-Agent does NOT match the correct fingerprint for Chrome. 100% of these hacking tools will not be able to access your website and will only ever be served a "Browser Verification JavaScript Challenge", similar to cloudflair. Real browsers pass through, 100% of bots are stopped.
Step 2, identify bots. There are 2 types of bots, good bots like googlebot, and bad bots like nmap, or zgrab. BitFire maintains a list of over 3,000 known good bots with matching IP and DNS authentication information. Good bots are authenticated and allowed, "Unknown Bots" have reputation data checked and a decision made based on IP reputation.
Make sure you verify your Bot Control panel after running BitFire for a few days.
- "Require Full Browser": This option will verify browsers are real humans by fingerprint or send a JavaScript challenge page. This option stops 99% of bot attacks which will show up in the dashboard as "Browser Check"
- "Allow Only Approved Bots": This option will verify that anything not identified as a browser, will be verified against the site bot list configuration. By default only verified good bots and high IP reputation IP addresses are allowed. Be sure to review the Bot Control configuration to make sure you haven't blocked any plugin access.
- "Block Hacking Tools": This option instantly block any bot connecting to your website with a User-Agent of a malicious tool like wpscan, nmap, etc.
- "Block Plugin & Theme Scans": This option will confuse plugin and theme scanners by detecting these scans and replying with random data for each plugin scanned. This will confuse any scanner and return bogus data for all scans.
- "Do Not Bot Check Ajax Requests": This option is only necessary for sites with page caching enabled and dynamic ajax requests on the user facing website. Page caching intercepts the normal browser verification step, sending an XMLHTTPRequest as the first seen request. For some sites also running behind a proxy, this can fool fingerprinting into thinking all requests are invalid. Enable this option if you have problems with AJAX requests for users.
- "Block Web Scrapers": By default, BitFire will allow any browser, or bot to access your site to view any page. Enabling this option requires all browsers and bots to verify before accessing any page, even if just for viewing
- "High Sensitivity Block Mode": This mode is restricted to users with Premium support. It changes the default block mode from reputation check (128 free reputation checks) / open, to always closed for unknown bots.
- "Challenge Style": Select which JavaScript challenge to display for browsers with unknown fingerprints. You can select a simple white page, spinner, BitFire verification screen, or emulate the cloudflair light and dark themes pages.